
Last week, Solana-based decentralized finance (DeFi) platform Drift Protocol, a perpetual futures platform on Solana, suffered a massive vault drain to the tune of $285 million. The attacker exploited the Drift Protocol by abusing a legitimate feature called 'durable nonces,' rather than exploiting a code bug or stolen keys.
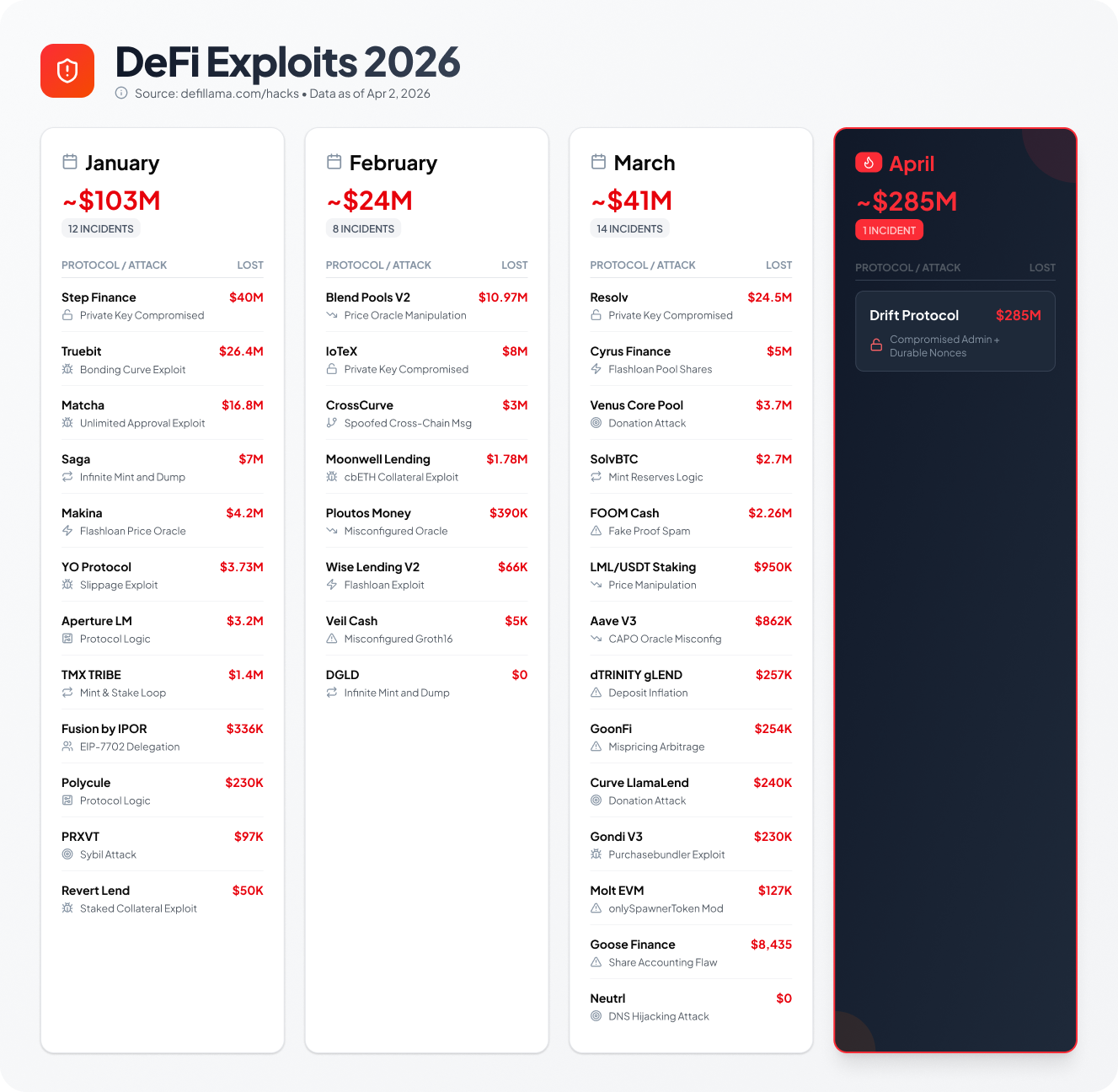
The previous week, the Resolv DeFi protocol was exploited when an attacker was able to mint tens of millions of Resolv’s unbacked stablecoins (USR) and extract roughly $23 million in value, forcing the protocol to halt operations. Sadly, this has been a recurring theme for Defi protocols and platforms in 2026.
According to DefiLlama data, the first quarter (Q1) of 2026 saw a significant, albeit ongoing, trend of hacks and security exploits in the DeFi ecosystem. While total losses were lower than the same period in 2025, hackers still stole over $168.6 million from 34 different DeFi protocols. And the Drift attack easily eclipses that total.
Looking for a Root Cause
Make no mistake, this was a sophisticated attack. Instead of finding a hidden bug in the computer code, the attacker used a "master key" method, stealing, or tricking the system into using, administrative permissions to empty the vaults in a matter of minutes.
The Setup: Stealing the Keys (Weeks Prior)
The "Master Key" (Multisig) Compromise: The protocol’s security setup required multiple trusted people ("signers") to approve major actions (a multisig wallet). The attacker somehow gained control of these high-level admin keys.
Pre-signed Traps ("Durable Nonces"): Instead of hacking in and doing everything at once, the attacker used a clever trick called "durable nonces". Think of this as getting a trusted manager to pre-sign a blank cheque weeks in advance. The attacker held these valid signatures until they were ready to use them.
The Attack: Emptying the Vault (April 1, 2026)
Creating a Fake "Token": The attacker used a worthless "fake" token to trick the system's internal price checkers, making it look like they were depositing something valuable.
Unlocking the Vaults: Using the stolen/pre-signed admin keys, the attacker changed the rules of the system (e.g., bypassing safety circuit breakers/withdrawal limits).
The Drain: Once the rules were changed, the attacker used those same keys to approve the withdrawal of real user funds—stablecoins, Bitcoin, and Solana—and moved them out of the vault. The theft, which affected all user deposits on Drift and routed funds through NEAR, Backpack, Wormhole and Tornado Cash, underscores how social engineering and operational failures—especially around durable nonce handling—are becoming a leading threat vector in DeFi.
What Can Be Done?
It’s quite apparent that the root cause of this exploit was a vulnerability in the smart contract protocol. It’s easy to say in hindsight that Drift should have done a better job of securing the protocol.
Experts agree that securing DeFi smart contracts requires a multi-layered "defense-in-depth" approach, integrating rigorous development standards, external validation, and post-deployment monitoring. The process involves securing the code throughout its entire lifecycle—from design to post-launch maintenance. This is not a trivial exercise as the checklist below suggests.
Summary Checklist for DeFi Security
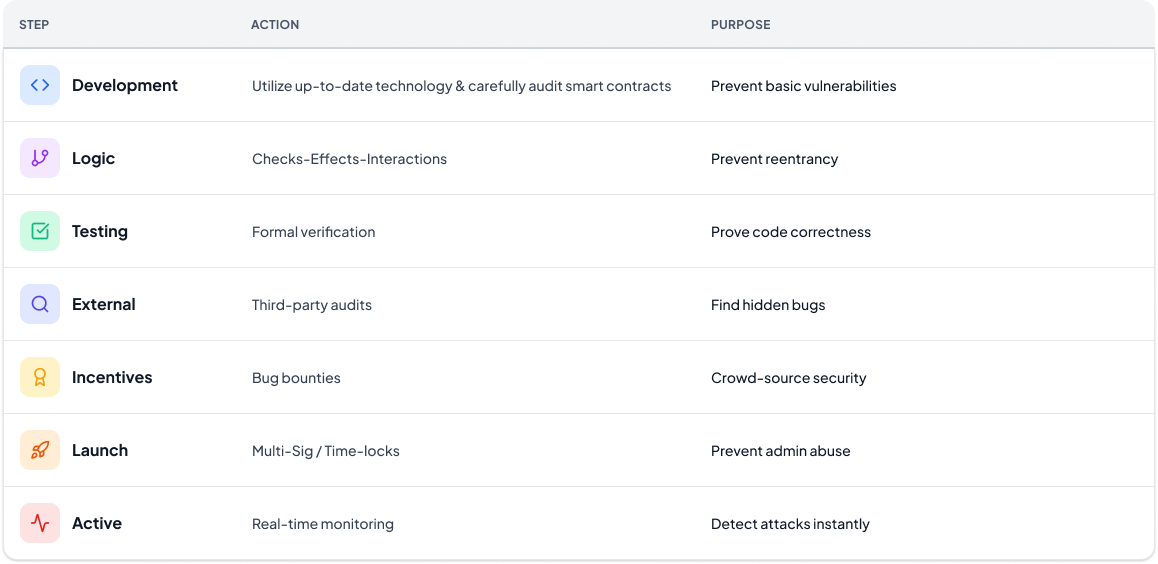
This should be considered table stakes but, this still only addresses just half of the solution.
The other half involves embedding checks and balances into these DeFi platforms and protocols which can serve as an early warning system.
The Shortcoming of Traditional Blockchain Analytic Tools
There are blockchain solutions that can help address part of this early warning system. Anything which posts to the blockchain should be leveraged to spot anomalies, but what’s really needed are solutions that evaluate pre-signature risk signals to help mitigate against these types of attacks. These pre-signature signals can detect the creation of zero-history wallets and alert you to funds transfers exceeding specific amounts so you have time to react.
I like to use home security systems as a parallel.
With a home security system, you will be alerted when an intruder breaks into your home and you may get a good look at the culprit. But, these systems do not prevent the bad actor from intruding (though they may trigger some alarms and summon the police). Sadly, by the time the police arrive, these intruders often have stolen your high-value goods and they’re long gone.
You’re way better protected having armed guards, along with roaming guard dogs, to prevent the intruder from ever breaking in. Traditional blockchain forensic solutions will sound the alarm only after the transaction has been posted to the blockchain — unfortunately, by then, the damage is done.
At Web3Firewall, we’re the armed security guards and roaming guard dogs protecting your property. We do this by analyzing 100+ risk pre-signature signals and equipping you with a robust policy engine that alerts and even stops transactions in their track if certain conditions are met (e.g., vault transfers exceed a specific dollar amount).
If you’re a DeFi platform and concerned about going adrift, let’s chat. If you want to dive deeper into the Drift exploit, check out this incident analysis.