Crypto payment screening is the risk-based review of blockchain wallet addresses and transactions before or during a crypto payment flow. It helps payment platforms identify sanctions, AML, fraud, and behavioral risk signals before funds are credited, released, or escalated for review. Unlike traditional payment screening, which relies on identity databases and card network rules, crypto payment screening operates on publicly available blockchain data including transaction history, counterparty relationships, and behavioral patterns. It is one component of a broader compliance and risk framework for organisations processing digital asset payments.
In one sentence:Crypto payment screening evaluates the on-chain history and behavioral patterns of a payment wallet before funds are processed — detecting risk signals invisible to traditional payment controls.
The core distinction:Traditional payment screening checks identity. Crypto payment screening checks on-chain behavior.
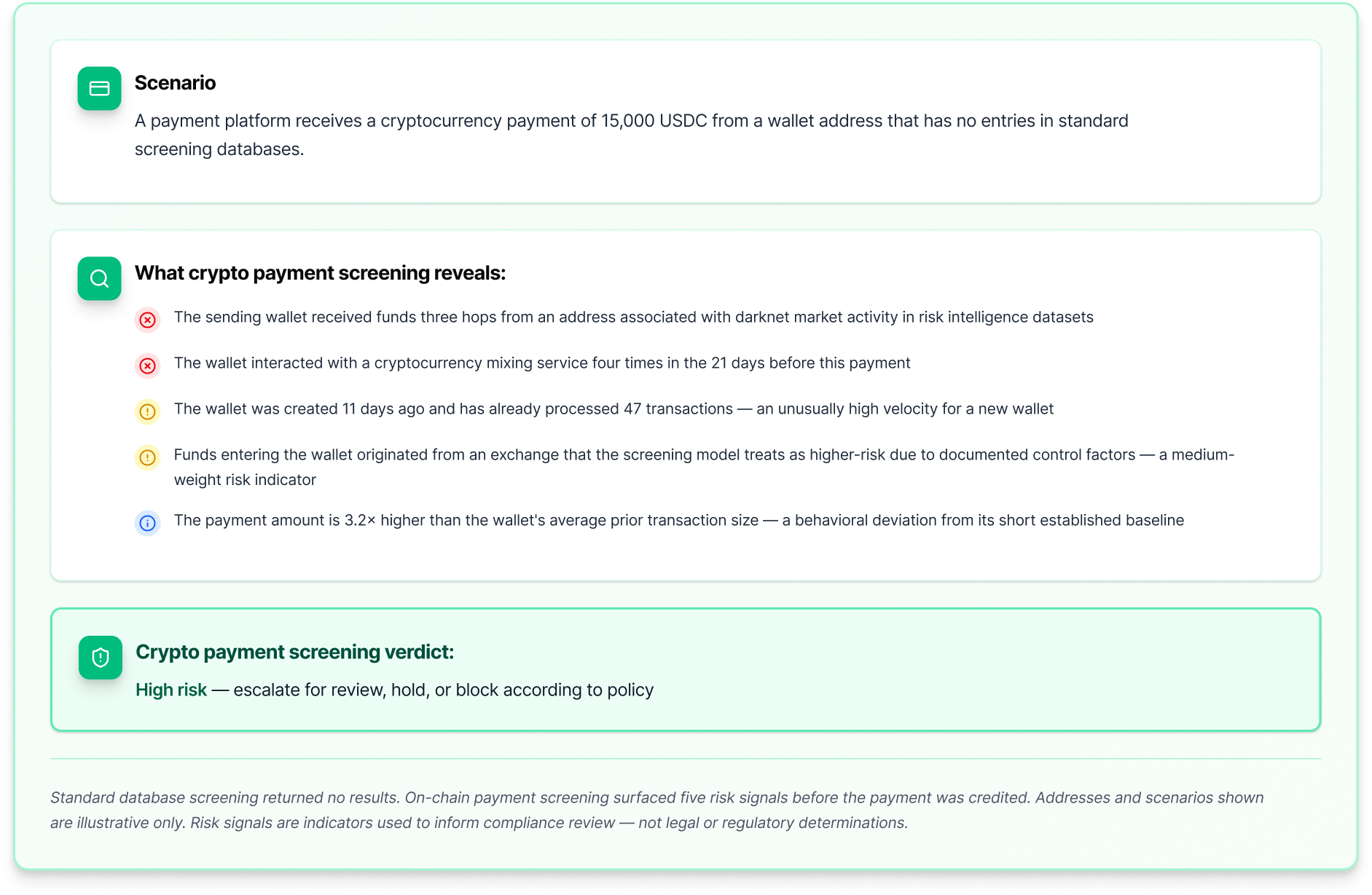
When a customer sends a cryptocurrency payment, the funds leave their wallet and travel across a public blockchain — often without any regulated intermediary involved. The payment platform receiving those funds typically knows the sending wallet address, but may know very little else about it. The wallet could have a clean history or a complex one. It could be freshly created or years old. It could have interacted with mixers, darknet markets, or high-risk entities at any point in its history.
Crypto payment screening is the discipline of answering those questions systematically — at the point of payment, before processing decisions are made. It uses publicly available blockchain data to reconstruct the payment wallet's transaction history, map its counterparty relationships, evaluate its behavioral patterns, and produce a structured risk assessment that informs whether the payment should be processed, flagged, or escalated.
The term covers several related activities: digital asset transaction monitoring, blockchain payment analysis, wallet screening, and — in pre-broadcast workflows — evaluating a payment transaction before it is submitted to the network. Tools performing these functions are used by crypto exchanges, payment processors, custodians, stablecoin issuers, and any other organisation that receives or sends value on a blockchain.
For organisations subject to AML/CFT obligations, crypto payment screening can support transaction monitoring, wallet-risk review, and investigative workflows relevant to Travel Rule and suspicious activity reporting obligations — but it is only one part of the broader control framework that regulated payment organisations are expected to maintain.