Why Web3Firewall for zero-history wallet risk
Request a demoWeb3Firewall is a Web3 security and compliance platform, often described as a SIEM for blockchain. It is designed for compliance and security teams who need wallet risk assessment to cover the full transaction population, including wallets for which standard history-based screening returns no usable signal.
The platform is designed to combine behavioral monitoring, wallet risk scoring, transaction simulation, and a programmable policy engine into a single operational layer. For zero-history wallets, the platform can shift assessment to contextual signals and pre-broadcast simulation of the transaction itself, rather than relying solely on accumulated transaction history. Transactions routed through Web3Firewall can receive a real-time verdict of allow, deny, or require approval, applying customer-defined risk and policy controls within configured workflows before a transaction reaches the network.
This enables organisations to apply proportionate, policy-driven scrutiny to the zero-history wallet population without treating every new wallet as high risk or returning a false clean result when no data is available.

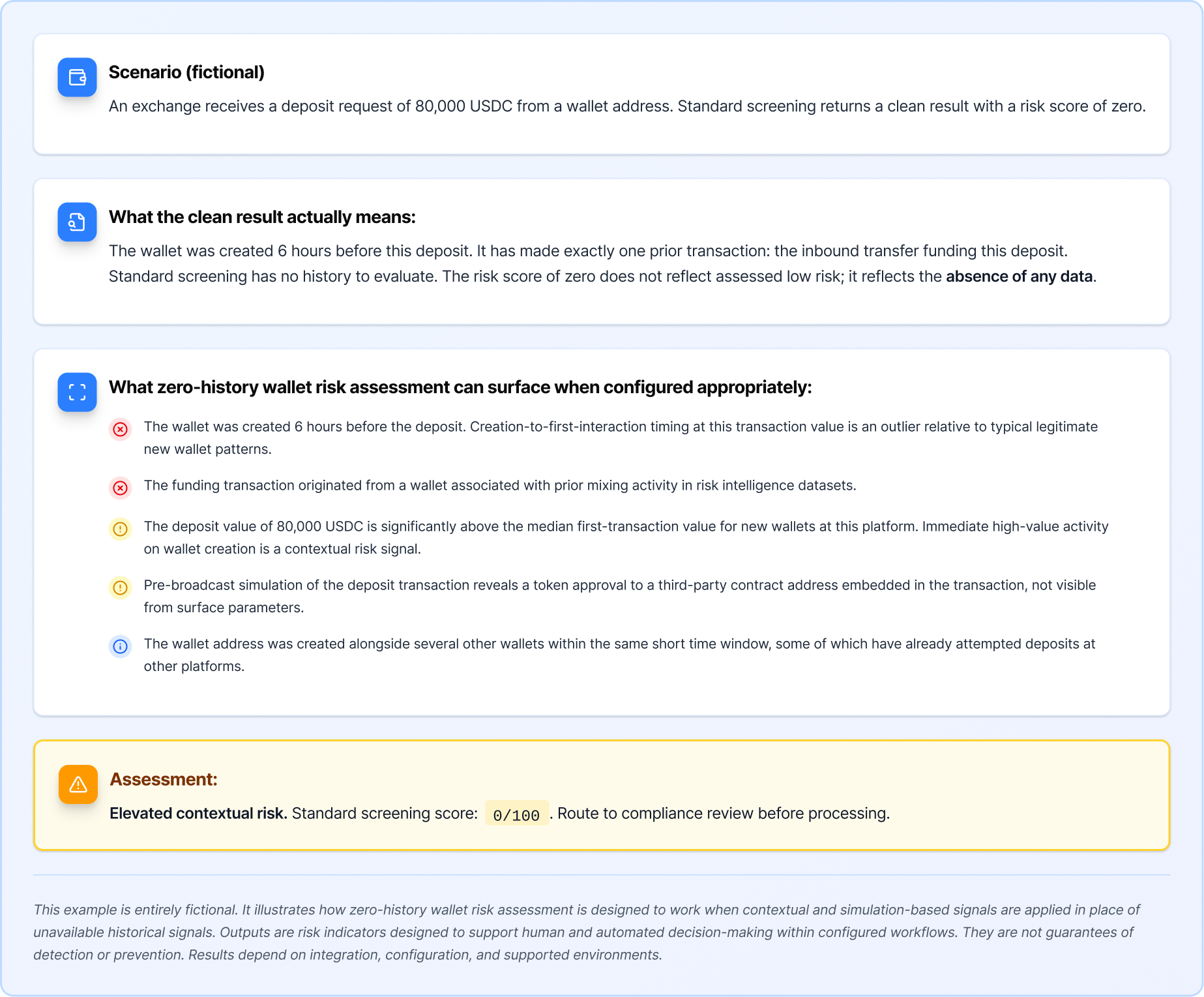
Contextual risk assessment for new wallets
When a wallet has no prior transaction history, risk assessment can be configured to draw on contextual signals available at transaction time: creation timing, funding source characteristics, first transaction value, asset type, and protocol interaction pattern. These signals may be combined into a contextual risk indicator even when historical signals are unavailable.

Pre-broadcast simulation independent of wallet history
Transaction simulation can evaluate the full execution path of a transaction before it reaches the network, regardless of whether the sending or receiving wallet has any prior history. Unexpected token approvals, unusual routing, interactions with flagged contracts, and economically anomalous state changes may all be detectable at simulation time from the transaction itself.

Coordinated new wallet activity detection
Wallet activity can be monitored to detect patterns where multiple zero-history wallets are created and begin transacting within a short time window, interacting with the same protocols or platforms. Such patterns may indicate coordinated infrastructure rather than independent new user activity, depending on configuration and supported environments.

Policy-driven controls for the zero-history population
Configurable policy controls can be set to apply heightened scrutiny to transactions involving zero-history wallets above defined value thresholds, routing them for manual review, requiring additional verification, or holding them pending approval within customer-defined workflows. This applies proportionate additional coverage to the population with limited screening data.

Funding source traceability
If a zero-history wallet has received an inbound funding transaction before the assessed transaction, the risk characteristics of that funding source can be incorporated into the assessment. A zero-history wallet funded by a high-risk address carries elevated contextual risk even without its own transaction history.

Audit-ready zero-history assessment records
Every zero-history wallet assessment, contextual signal evaluation, and transaction verdict can be logged with supporting evidence. Compliance teams can maintain an auditable record of how zero-history wallet transactions were assessed, what signals were available, and what decisions were made, for regulatory examinations and governance reviews.
Web3Firewall provides risk intelligence and analysis tools. It does not provide legal, regulatory, or investment advice. Risk signals and assessment outputs are indicators designed to support human and automated decision-making within configured workflows. They are not guarantees of detection or prevention outcomes. Results depend on integration, configuration, and supported environments.