RWA security refers to the monitoring, smart contract analysis, transaction intelligence, and risk controls used to protect tokenized real-world assets (RWAs) operating on blockchain networks. It covers the full digital layer of tokenized asset infrastructure — including the smart contracts that govern ownership and transfers, the wallets that hold and interact with tokens, and the blockchain transactions that record asset movements. As tokenized asset activity grows, RWA security becomes a more important operational requirement for issuers, custodians, and infrastructure providers.
In one sentence:RWA security protects the smart contract and transaction layer where tokenized real-world assets live — adding blockchain-specific controls to the institutional and operational security that tokenized asset operations already require.
The core distinction:Traditional asset security protects custodians and registries. RWA security also protects the smart contracts and wallets that encode and control asset ownership on-chain.
When a real-world asset is tokenized, its ownership and transfer logic moves onto a blockchain — encoded in smart contracts that execute automatically based on predefined rules. A tokenized treasury bond, for example, is no longer just a record in a custodian's ledger. It is a smart contract that defines who holds it, under what conditions it can be transferred, and what events trigger payments or redemptions.
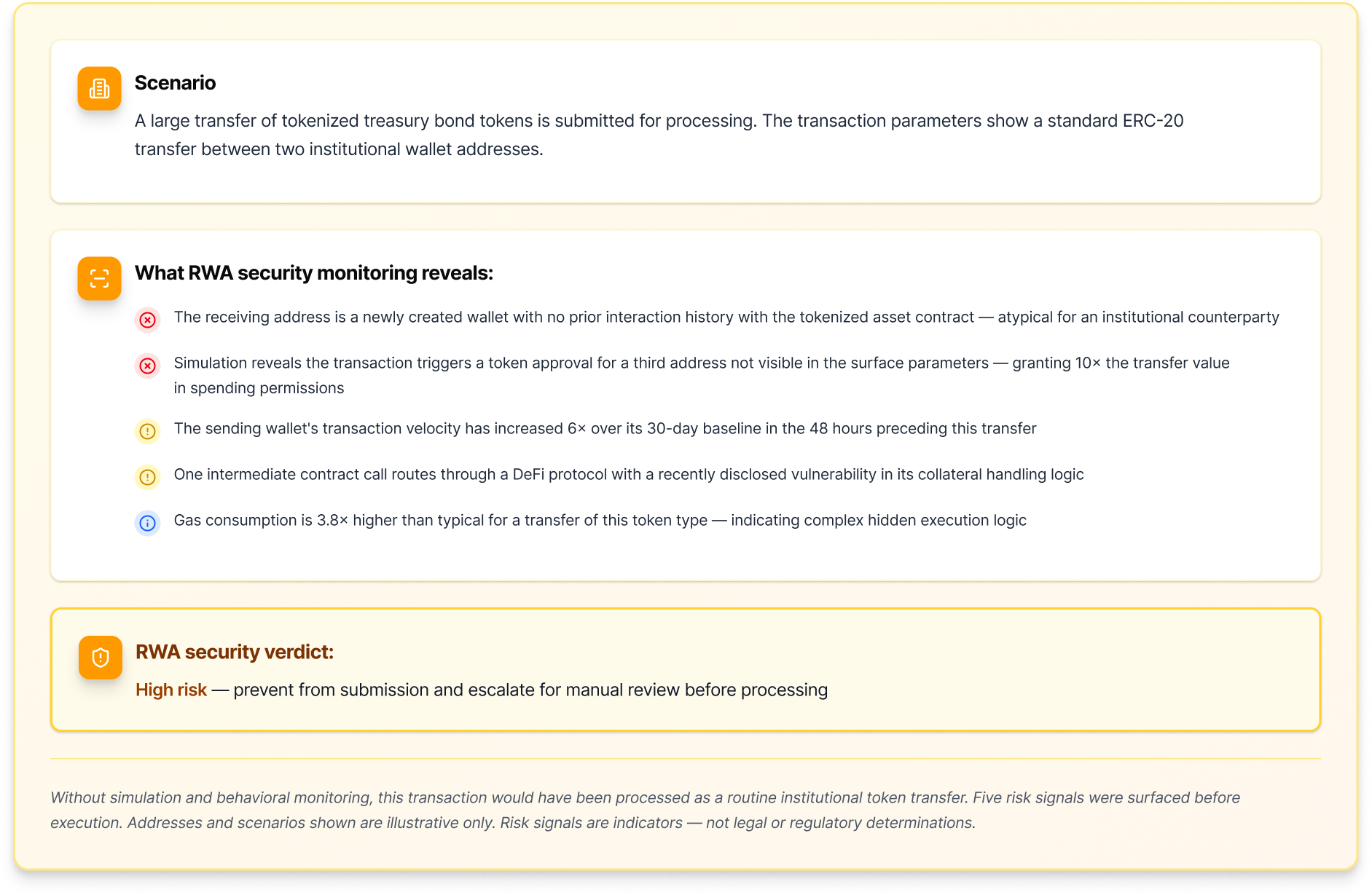
RWA security is the practice of monitoring and protecting this digital layer. It encompasses continuous analysis of the smart contracts that manage tokenized assets, the wallets that hold them, and the transactions that move them — across both the primary issuance environment and any DeFi protocols the tokens interact with.
The scope of RWA security is expanding in line with the market. As tokenized RWAs integrate with DeFi lending protocols, liquidity pools, and cross-chain bridges to access deeper capital markets, the security surface grows proportionally. A tokenized asset that interacts with a DeFi lending protocol is now exposed not just to risks in its own smart contracts, but to vulnerabilities in every protocol it touches.
For organisations operating tokenized asset infrastructure, RWA security requires the same capabilities as broader blockchain security — behavioral monitoring, transaction simulation, smart contract analysis, and policy controls — applied specifically to the high-value, institutionally sensitive context of real-world asset tokenization.