
What Is Crypto Transaction Simulation in Blockchain?
Crypto transaction simulation predicts exactly how a blockchain transaction will execute — its contract calls, token flows, and state changes — before it is broadcast to the network, creating an intervention window that does not exist after confirmation.
Quick Answer: What is crypto transaction simulation?
Crypto transaction simulation is the process of evaluating how a blockchain transaction will execute — including its smart contract interactions, token transfers, state changes, and gas consumption — before it is broadcast to the network. It creates a pre-execution window for risk assessment and enforcement, enabling teams to allow, deny, or escalate transactions before they become irreversible on-chain.
When combined with a risk scoring and enforcement layer, simulation becomes more than analysis — it becomes a decision point. A transaction routed through a simulation layer that registers as high-risk can be prevented from submission, held, or escalated for review before it ever reaches the network. This is the foundation of pre-broadcast risk enforcement in blockchain security operations.
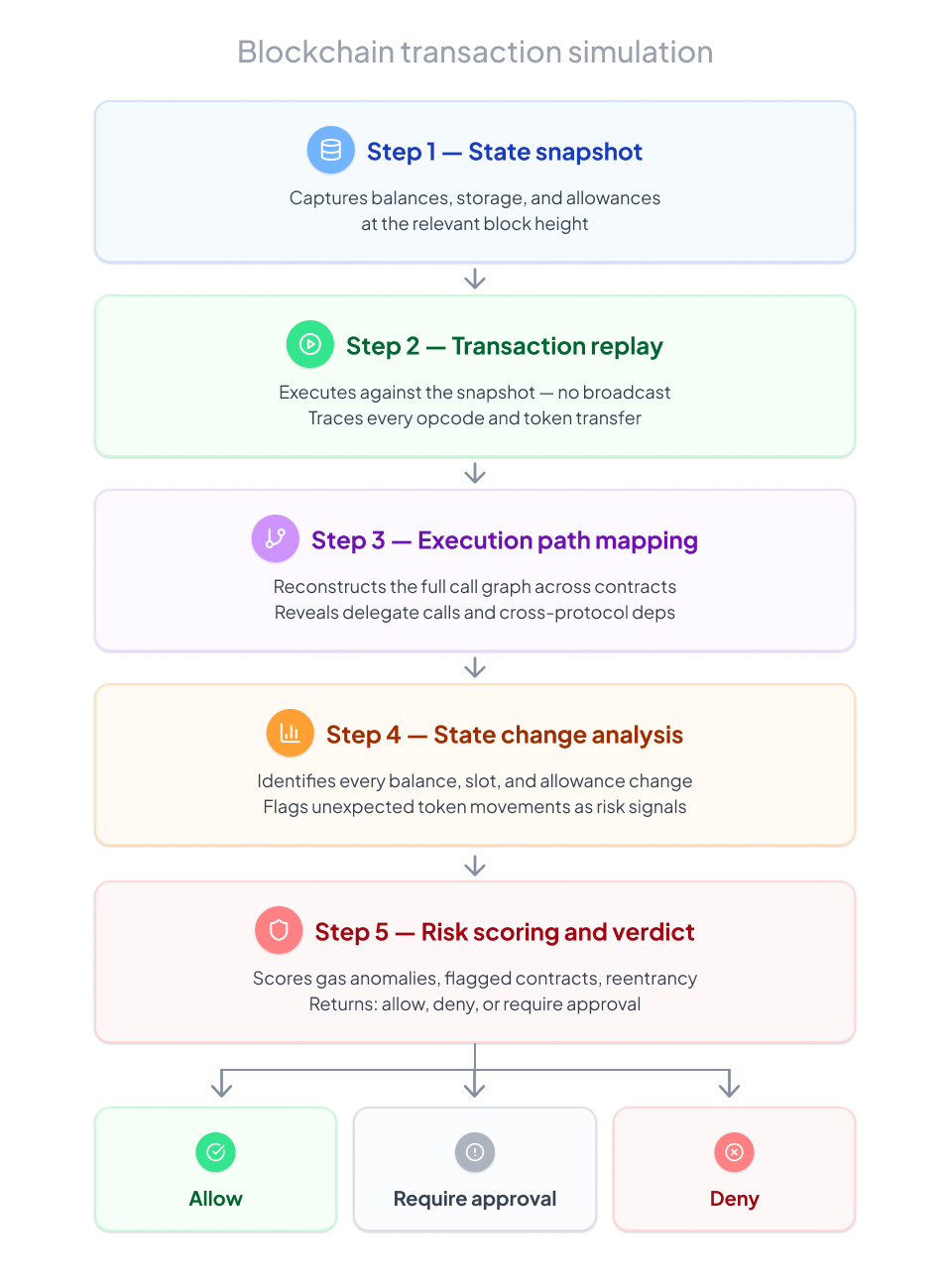
Crypto transaction simulation — including Ethereum transaction simulation and simulation across other EVM-compatible chains — replicates the execution environment against a snapshot of the current blockchain state. The process runs in five steps:
A well-configured crypto transaction simulation engine surfaces the following risk signals before a transaction is submitted to the network:
Unexpected Token Transfers: Token movements not present in the transaction's stated intent — including transfers to unexpected addresses, unauthorized approval consumption, or abnormal transfer volumes relative to the transaction type.
Unauthorized State Changes: Smart contract storage modifications that deviate from expected behavior — including changes to ownership variables, access control settings, or protocol configuration parameters.
High-Risk Address Exposure: Execution paths that route through addresses associated in risk intelligence datasets with sanctions exposure, exploit activity, or other elevated risk, including indirect interactions within supported environments.
Re-Entrancy-Consistent Call Patterns: Re-entrancy in smart contracts occurs when a function makes an external call to an untrusted contract before it resolves its internal state, allowing the untrusted contract to recursively call back into the original function.
Abnormal Gas Consumption: Gas usage disproportionate to the transaction's apparent function — often indicating that complex hidden logic is executing inside what appears to be a simple call.
Oracle Manipulation Setup Patterns: Execution paths that include price-sensitive reads from oracle or AMM pool contracts immediately after a large liquidity movement — a pattern consistent with oracle manipulation setups.
Flash Loan Interaction Patterns: Transactions that borrow and repay within the same execution — particularly those involving large amounts relative to pool liquidity combined with price-sensitive contract calls.
Cross-Contract Dependency Chains: Deep call graphs involving multiple protocols in sequence — bridges, DEXs, lending protocols, liquidity pools — that create complex execution dependencies and expand the risk surface of a single transaction.
Approval and Allowance Manipulation: Token approval transactions granting unexpectedly large or unlimited spending permissions to contracts or addresses that do not match the transaction's stated purpose.
Simulation cannot guarantee prevention, but it provides a pre-execution enforcement window that does not exist with monitoring alone. Transactions that exhibit high-risk execution patterns — re-entrancy, oracle manipulation setups, flash loan abuse — can be denied before they reach the network.
EVM transaction simulation works across Ethereum and EVM-compatible chains (Polygon, Arbitrum, Base, BNB Chain, etc.). Non-EVM chains require chain-specific simulation implementations.
No. A test transaction uses a test network and consumes real gas on that network. Crypto transaction simulation runs against the live blockchain state without submitting anything to any network — no gas is consumed, and the transaction is never broadcast.
Web3Firewall's simulation engine is designed for near real-time operational use within supported environments. Ask for our API documentation for performance specifications.
Crypto transaction simulation and transaction monitoring are complementary capabilities that operate at different points in the transaction lifecycle. The distinction matters because they address fundamentally different risks.
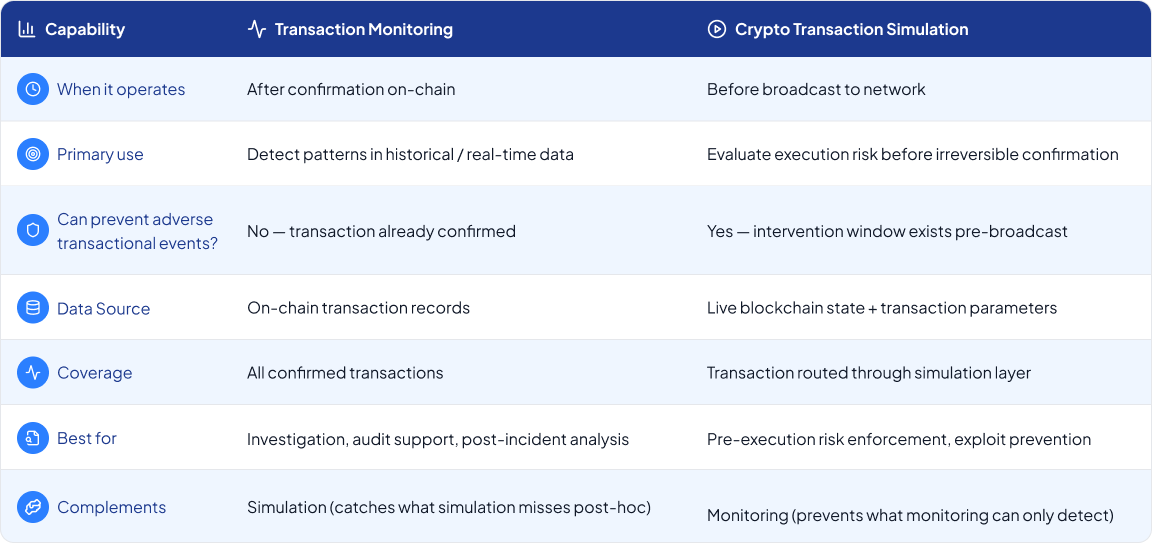
In other words, transaction monitoring tells you what happened, while transaction simulation tells you what will happen — and gives you the ability to stop it.
For organizations where the cost of a single bad transaction is high — exchanges processing large withdrawals, custodians handling institutional assets, DeFi protocols with significant TVL — simulation is the difference between prevention and incident response.
Address poisoning is one of the most effective social engineering attacks in crypto operations precisely because it exploits visual verification habits. An attacker deploys a wallet address with a matching prefix and suffix to a legitimate address in the victim's transaction history. The full address is different — but in every interface that truncates the middle, it looks identical.
Here is what pre-broadcast crypto transaction simulation and destination screening surfaces before an outbound transfer that would otherwise appear routine:
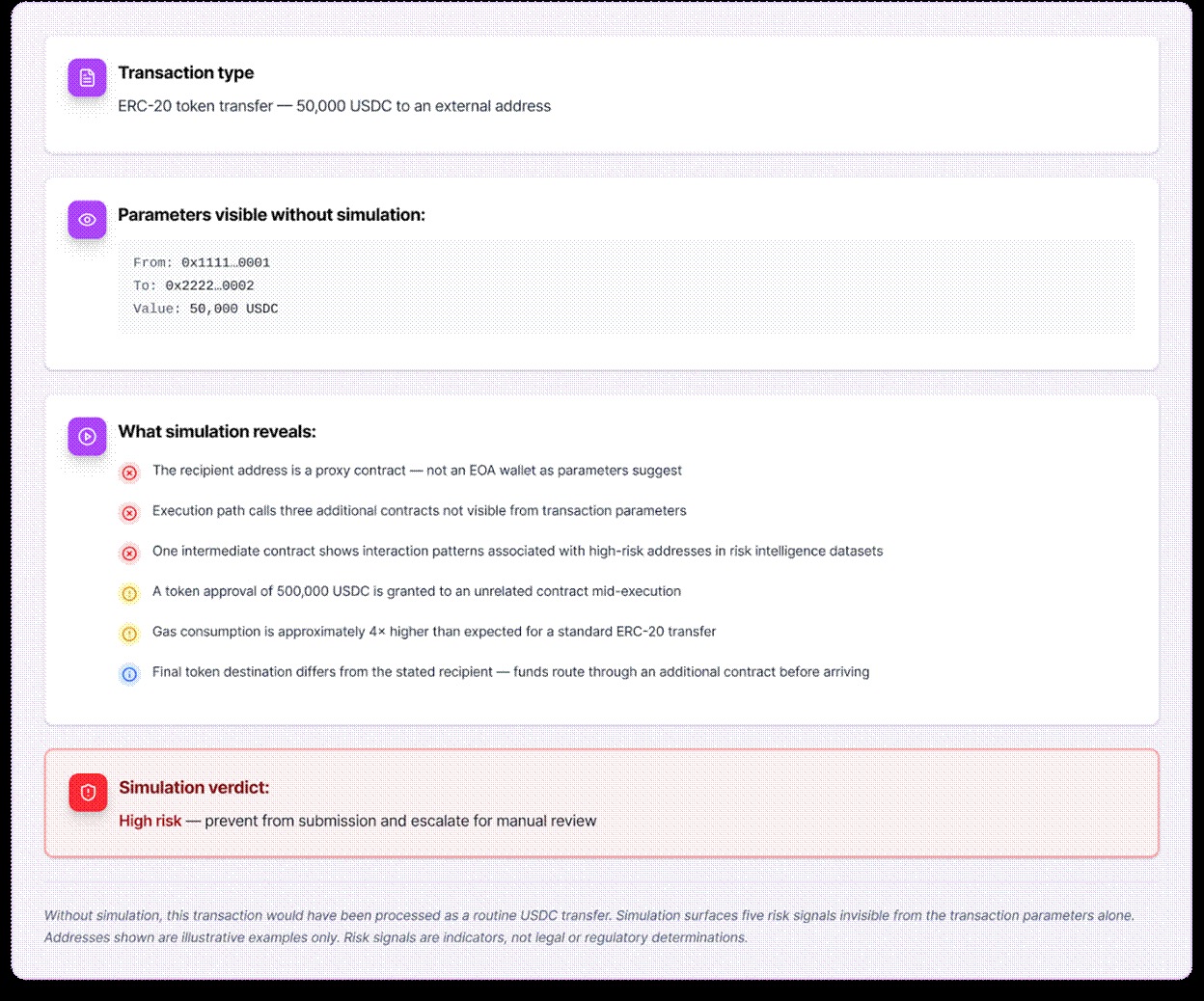
This example illustrates why address poisoning is so effective against teams that rely on visual verification alone. A full address with a matching prefix and suffix looks identical to the legitimate address in every interface that truncates the middle. Verification must be systematic, not visual. Pre-broadcast destination screening configured for crypto transaction simulation catches this before funds move.
Web3Firewall is a Web3 security and compliance platform — purpose-built for operational teams who need risk decisions at machine speed. Most crypto transaction simulation tools were built for developers — useful for testing contract behavior but not designed to operate as a live enforcement layer.
Web3Firewall's simulation engine was built for operations: it runs on transactions routed through the platform in near real time, feeds into an automated verdict system, and integrates with compliance workflows supporting MiCA-oriented compliance workflows, NIST, and OWASP frameworks.
Transactions routed through Web3Firewall are simulated before broadcast within supported environments. The simulation output feeds a real-time verdict — allow, deny, or require approval — that enforces policy decisions before the transaction reaches the network.
Simulation results feed directly into a real-time decision engine. Transactions that simulate as high-risk receive an automated verdict — allow, deny, or require approval — before submission. Not a reporting tool. It provides a vital enforcement layer for configured workflows.
Full Execution Path Tracing
Every function call, external contract interaction, token transfer, and state change is traced across the complete call graph within supported environments — including deeply nested cross-protocol interactions invisible from transaction parameters alone.
Integrated Risk Scoring
Simulation outputs are scored against Web3Firewall's risk model — combining execution path signals with wallet risk scores, high-risk address screening, and behavioral baselines to produce a unified pre-execution risk assessment.
Programmable Enforcement Policies
Define simulation-based enforcement policies in a no-code interface or via API. Policies can be transaction-type-specific, asset-specific, or counterparty-specific. The enforcement layer adapts to your risk framework.
Compliance-Ready Simulation Logs
Every simulation run is logged with execution details, risk signals, verdict, and supporting evidence. These logs are designed to support regulatory reporting workflows and internal governance reviews. Nothing in these logs constitutes a legal or regulatory determination.
API Integration for Existing Workflows
Web3Firewall's crypto transaction simulation API integrates into existing transaction processing pipelines — exchanges, custodians, DeFi protocols, and infrastructure providers. Designed for near real-time operational use, not batch processing.
Crypto transaction simulation evaluates how a blockchain transaction will execute before it is broadcast — tracing contract calls, token flows, and state changes against live chain state.
Unlike transaction monitoring, simulation operates pre-broadcast and can prevent high-risk transactions from reaching the network.
EVM transaction simulation works across Ethereum and EVM-compatible chains, and is the foundation of pre-execution risk enforcement in blockchain security.
Web3Firewall runs simulation in near real time as an enforcement layer — not a developer testing tool — producing allow/deny/escalate verdicts before transactions are submitted.
Key risks detected: unexpected token transfers, unauthorized state changes, re-entrancy patterns, oracle manipulation setups, flash loan abuse, approval manipulation, and high-risk address exposure.
To learn more about transaction simulations, check out this resource page on our website.
Disclaimer: Web3Firewall provides risk intelligence and analysis tools. It does not provide legal, regulatory, or investment advice. Detection outputs are risk indicators designed to support human and automated decision-making within configured workflows. They are not guarantees of detection or prevention outcomes. Results depend on integration, configuration, and supported environments.