

Crypto payment screening (also called blockchain payment screening) is the risk-based review of blockchain wallet addresses and transactions before or during a crypto payment flow. It identifies sanctions, AML, fraud, and behavioral risk signals before funds are credited or released — helping payment platforms avoid irreversible exposure to illicit activity.
In October 2025, FinCEN designated Huione Group as a primary money laundering concern under Section 311 of the USA PATRIOT Act. The group processed over $98 billion in cryptocurrency inflows between 2021 and 2025, including more than $4 billion in confirmed illicit proceeds.
Huione Pay — Cambodia's digital payments arm and a key node in a vast scam-driven financial ecosystem — routed flagged funds to major exchanges including Binance and OKX. After a bank run by panicked users, Huione Pay froze withdrawals and shut down, closing what blockchain analysts called the world's largest illicit online marketplace.
The critical lesson: Huione's funds passed through legitimate payment rails because crypto payment screening either happened too late or not at all. This post explains how to screen digital asset payments effectively — before it's too late.
Crypto payment screening — also called digital asset payment monitoring or blockchain payment screening — is the systematic, risk-based review of blockchain wallet addresses and transaction data at the point of payment.
When a customer sends a cryptocurrency payment, the funds leave their wallet and travel across a public blockchain — often without a regulated intermediary. The receiving platform typically knows the sending wallet address, but may know very little else:
• Does the wallet have a clean history or a complex one?
• Has it interacted with mixers, darknet markets, or sanctioned entities?
• Was it freshly created or years old?
• Does its behavioral pattern match legitimate payment wallets?
Crypto payment screening answers these questions systematically — using publicly available blockchain data to reconstruct transaction history, map counterparty relationships, evaluate behavioral patterns, and produce a structured risk assessment.
Traditional payment screening was built for closed networks — card schemes, correspondent banks, and regulated payment processors where every participant is identified and every transaction can be reversed. Blockchain payment screening operates in a fundamentally different environment.
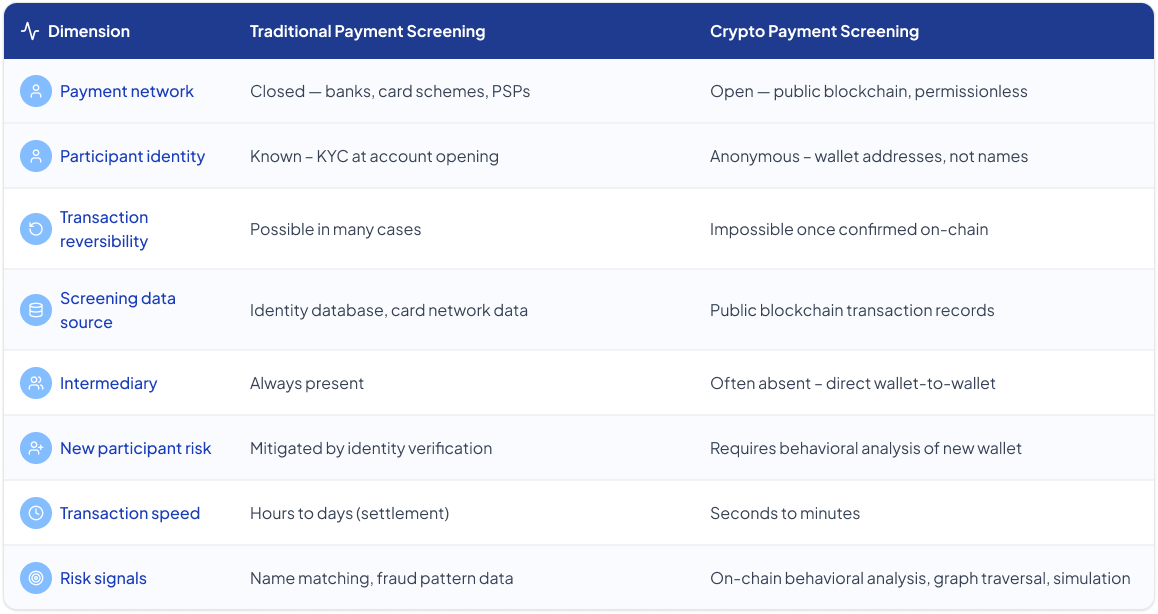
The two most operationally significant differences: irreversibility and the absence of intermediaries. In traditional payments, a suspicious transaction can often be reversed, recalled, or frozen. In crypto, a confirmed payment is permanent — placing much greater weight on pre-processing screening. And because there is no card network or correspondent bank applying its own controls, every organization in the crypto payment chain must apply its own screening.
A well-designed crypto payment screening system operates across four stages:

Static watchlists and known-bad address databases only identify wallets that have already been flagged. By the time a wallet appears on a watchlist, the activity that triggered the flag has already occurred — and a significant proportion of payment risk originates from wallets with no prior flags at all.
Key Insight
Behavioral analysis extends crypto payment screening coverage beyond what static lists can reach. Rather than asking only "Is this address on a list?" it asks: "Does this wallet behave like legitimate payment wallets typically behave?"
• Transaction patterns and counterparty diversity
• Protocol usage across DeFi, bridges, and lending platforms
• Activity timing and velocity anomalies
• Deviations from a wallet's established baseline
This is especially relevant for self-hosted (unhosted) wallets, which may have limited history but can still exhibit detectable behavioral patterns that signal elevated risk.
Crypto payment screening identifies patterns consistent with a range of risk typologies. These are indicators — not legal or regulatory determinations.
1. High-Risk Address Exposure
Direct or indirect connections to addresses associated with sanctions-related activity, darknet market use, ransomware payments, or exploit-related fund flows in risk intelligence datasets.
2. Mixer and Obfuscation Service Use
Interactions with cryptocurrency mixing services or privacy protocols designed to break the transaction trail. This is a high-weight signal in most crypto payment screening risk models.
3. Layering and Structuring Patterns
Transaction sequences designed to obscure the origin of funds — including rapid movement across multiple wallets before the payment arrives, or amounts structured to fall below threshold levels.
4. Cross-Protocol Fund Routing
Funds that passed through multiple DeFi protocols, bridges, or lending platforms before arriving at the payment wallet — creating complex provenance chains that expand blockchain payment screening complexity.
5. Anomalous Transaction Velocity
Unusual spikes in transaction frequency immediately before or after a payment — consistent with automated fund consolidation, structuring, or rapid extraction activity.
6. Dormant Wallet Reactivation
Long-inactive wallets that suddenly initiate or receive large payments — associated with pre-planned fund distributions, coordinated activity, or compromised wallet recovery.
7. New Wallet High-Value Activity
Newly created wallets with minimal transaction history that immediately send or receive large payment values — a pattern that warrants behavioral review even without historical risk flags.
8. Exchange Risk Exposure
Funds that transited through exchanges treated as higher-risk due to control, exposure, or jurisdictional factors carry elevated risk signals — even if those exchanges are not themselves sanctioned entities.
9. Behavioral Baseline Deviation
Any significant departure from a wallet's established payment patterns in size, frequency, counterparty type, or protocol usage that warrants review regardless of whether known-bad indicators are present.
Example: Crypto payment screening signals in practice
Here is a concrete example of what crypto payment screening surfaces for a payment that appears routine from its surface parameters.
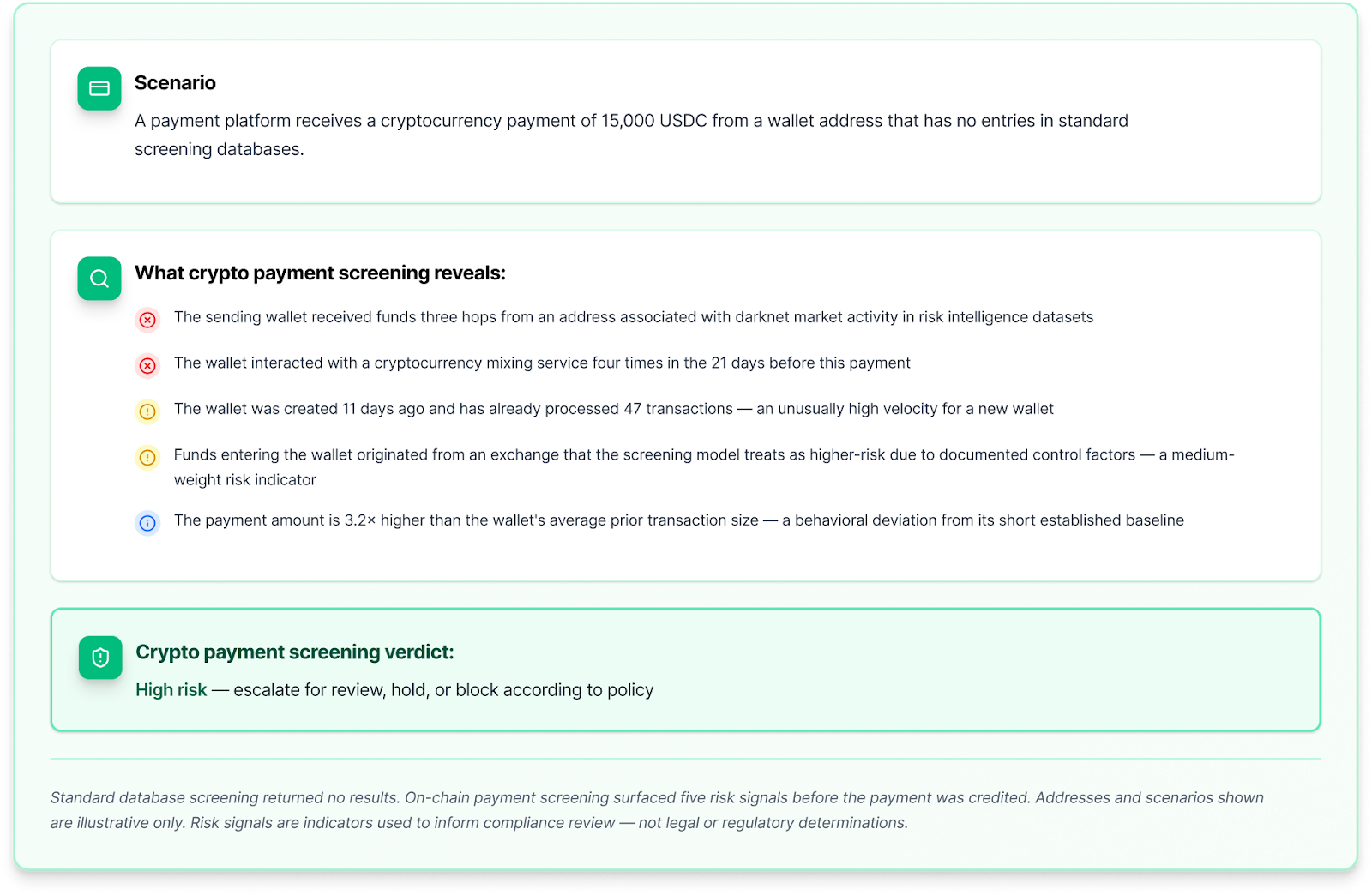
This example illustrates the core gap that crypto payment screening fills: a clean screening database result tells you a wallet hasn't been flagged before. On-chain behavioral screening tells you what the wallet has been doing. For payment platforms where a single high-risk payment can create regulatory exposure, both dimensions are necessary.
Q: What is crypto payment screening?
Crypto payment screening is the risk-based review of blockchain wallet addresses and transactions before processing a crypto payment. It uses on-chain behavioral analysis and counterparty graph traversal to detect AML, sanctions, fraud, and behavioral risk signals.
Q: How is blockchain payment screening different from traditional AML screening?
Traditional AML screening relies on identity verification and closed payment networks where transactions can be reversed. Blockchain payment screening operates on open, permissionless networks where participants are largely anonymous and transactions are irreversible — requiring behavioral analysis of wallet history rather than identity matching.
Q: When should crypto payment screening happen?
Crypto payment screening should happen before funds are credited or broadcast on-chain (pre-signature or pre-broadcast screening). Because confirmed blockchain transactions are irreversible, post-transaction screening provides limited remediation options.
Q: What is graph traversal in crypto payment screening?
Graph traversal traces fund flows across multiple hops to identify indirect exposure to high-risk counterparties. A payment wallet may not directly interact with a problematic address, but funds may have passed through intermediary addresses earlier — invisible from a single-hop check.
Q: Can crypto payment screening detect pig butchering scams?
Yes. Pig butchering victims typically make escalating deposits in a short window. A pre-signature blockchain payment screening monitor can detect a user who rarely made large crypto transfers suddenly sending multiple large stablecoin transactions to the same address cluster — a strong behavioral signal for social engineering fraud.
The Huione Pay case illustrates exactly what crypto payment screening can prevent. Had pre-signature screening been in place, several alarm bells would have fired:
The core gap crypto payment screening fills: A clean screening database result tells you a wallet has not been flagged before. On-chain behavioral screening tells you what the wallet has actually been doing. For payment platforms where a single high-risk payment creates regulatory exposure, both dimensions are necessary.
Blockchain payment screening tools are used by any organization that receives or sends value on a public blockchain, including:
To learn more about crypto payment screening and blockchain payment screening solutions, visit our Use Case page.