
At a glance
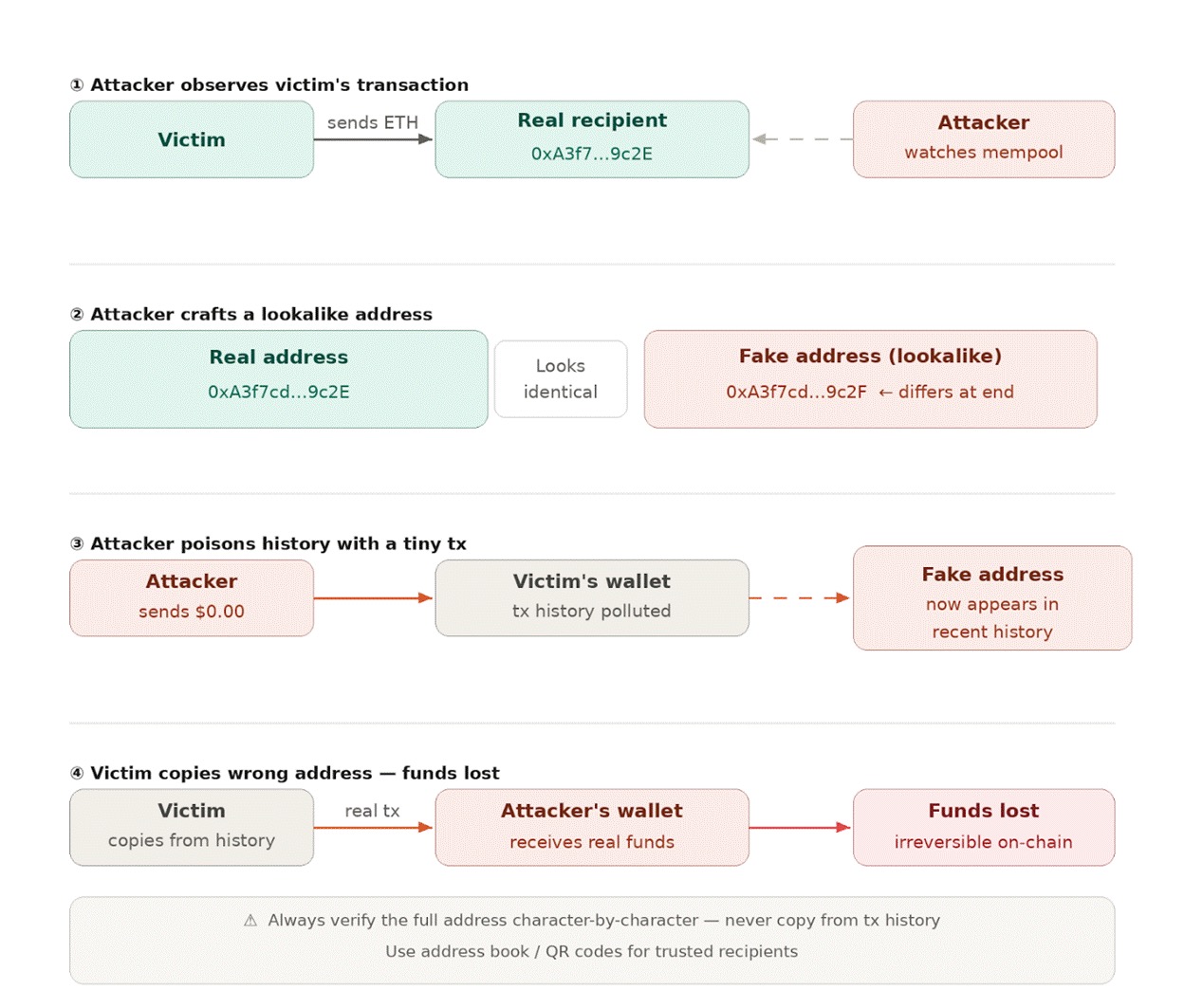
Address poisoning is a cryptocurrency scam in which an attacker sends a tiny transaction — often worth fractions of a cent — from a wallet address engineered to closely resemble one the victim regularly uses. The goal is to insert the fake address into the victim's transaction history, where it sits alongside legitimate entries and waits to be copied by mistake.
Because most wallet interfaces display only the first four to five and last four to five characters of an address, the spoofed address looks identical at a glance. The middle section — where it differs — is hidden. When the victim next sends a payment and copies what they think is a trusted address from their history, the funds go to the attacker instead.
Address poisoning is sometimes called a dusting attack, a wallet address poisoning attack, or a transaction history spoofing attack. All refer to the same core technique.
On December 20, 2025, a cryptocurrency trader lost approximately $50 million in Tether (USDT) in a single transaction — one of the largest single-user losses of the year. Here is exactly how the attack unfolded:
This attack follows a pattern also seen in the theft of approximately $24 million in aEthUSDC from a high-profile influencer known as "sillytuna" — demonstrating that high-value wallets are actively monitored and systematically targeted.
Address poisoning exploits human behavior, not a technical vulnerability in the blockchain itself. Crypto addresses are 40 or more hexadecimal characters long. Most people reasonably avoid retyping them by hand — they copy from transaction history instead. Attackers weaponize this habit.
Step 1 — Identify a target. Automated bots scan the blockchain for wallets that regularly send large transactions.
Step 2 — Generate a lookalike address. The attacker creates a wallet whose first and last few characters match the victim's usual recipient address. The middle characters differ, but wallet UIs hide them.
Step 3 — Send the dust transaction. A tiny amount of crypto (often zero or near-zero value) is sent from the lookalike address to the victim's wallet. This plants the fake address in the victim's history for a cost of a few cents in gas fees.
Step 4 — Wait. The attacker waits for the victim to copy the wrong address from their history and send a real transaction.
Step 5 — Collect. Once the victim sends funds to the spoofed address, the transaction is confirmed on-chain and irreversible. The attacker moves quickly to convert and mix the funds.
Address poisoning takes several forms, each targeting a slightly different vulnerability or user behavior:
The most common form. The attacker creates an address that matches the first and last characters of a legitimate recipient, then sends a zero or near-zero-value transaction to the victim. When the victim later scrolls their transaction history, they may copy the scammer's address instead of the real one.
On networks such as Ethereum and Tron, attackers send counterfeit tokens from a spoofed address, making it appear as though the victim initiated or authorized a transaction to the attacker's wallet. This manipulates the victim's on-chain record to normalize the fake address.
Automated scripts flood a target wallet with tiny transfers from the spoofed address repeatedly, making the fraudulent address appear multiple times in the transaction history and increasing the likelihood the victim will copy it.
A variation that pairs a poisoned address with malware. The malicious software monitors the clipboard and silently replaces any correctly copied wallet address with the attacker's lookalike address at the moment of paste.
Attackers send worthless or counterfeit tokens from an address spoofing a well-known decentralized exchange or trusted contact, hoping to lure victims into interacting with the fraudulent token contract.
Using tools to register Ethereum Name Service (ENS) domains or similar human-readable identifiers that closely mimic popular ones, attackers cause users to resolve and send funds to a fraudulent address instead of the intended recipient.
User education is the first line of defense. Anyone sending cryptocurrency should follow these habits:
Address poisoning is most effectively stopped at the pre-broadcast stage, before a transaction is submitted to the network. Once a transaction is confirmed on-chain, it is irreversible. Post-transaction monitoring can identify a poisoning pattern, but cannot recover funds. Pre-broadcast controls create the only reliable intervention window.
Platform operators should implement the following controls:
Pre-signature transaction screening is the most reliable technical intervention point available to operators today. For a deeper look at implementation, see our Address Poisoning resource page.
No. Once an address poisoning attack succeeds and the victim sends funds to the attacker's wallet, the transaction is confirmed on-chain and cannot be reversed. Blockchain transactions are final. The only recourse is to contact law enforcement, attempt on-chain communication with the attacker (as seen in white-hat bounty cases), or work with blockchain analytics firms to trace and potentially freeze funds at exchanges.
Look for unfamiliar micro-transactions in your wallet history — small amounts (often 0 or near-zero value) sent to you from addresses you do not recognize. These are the "dust" transactions used to insert a lookalike address. Most wallet software does not flag these by default, so periodic review of incoming transactions is important, especially for high-value wallets.
Address poisoning attacks have been documented on Ethereum, Tron, Bitcoin, and other networks where wallets display truncated addresses. Networks with low gas fees — making dust transactions nearly costless for attackers — are particularly attractive targets. Tron-based USDT wallets have seen a high volume of address poisoning incidents due to the combination of high transaction values and low fees.
The terms are often used interchangeably, but they are not identical. A dusting attack refers specifically to the act of sending tiny ("dust") transactions to a wallet, which is the delivery mechanism for address poisoning. Address poisoning is the broader fraud: the creation of a lookalike address, the delivery of the dust transaction to insert it into history, and the subsequent theft. Not all dusting attacks are address poisoning attacks — some dusting is used for wallet tracking or deanonymization rather than theft.
Address poisoning inserts a fraudulent address into a user's transaction history through a dust transaction, relying on the user to copy it by mistake. Clipboard hijacking uses malware installed on a device to intercept and replace a correctly copied address in real time. Both result in funds being sent to an attacker's wallet, but clipboard hijacking requires malware, while address poisoning requires no software on the victim's device.
For a comprehensive technical guide to address poisoning and how pre-signature transaction screening can prevent these exploits before funds move, visit our Address Poisoning resource page.