Why Web3Firewall for transaction simulation
Request a demoWeb3Firewall is a Web3 security and compliance platform — often described as a SIEM for blockchain. It is designed for operational teams who need risk decisions at machine speed, not developers running batch analyses in staging environments.
Most transaction simulation tools were built for developers — useful for testing contract behavior but not designed to operate as a live enforcement layer. Web3Firewall's simulation engine was built for operations: it runs on transactions routed through the platform in near real time, feeds into an automated verdict system, and integrates with compliance workflows designed to support controls relevant to MiCA-oriented compliance workflows, NIST, and OWASP frameworks.
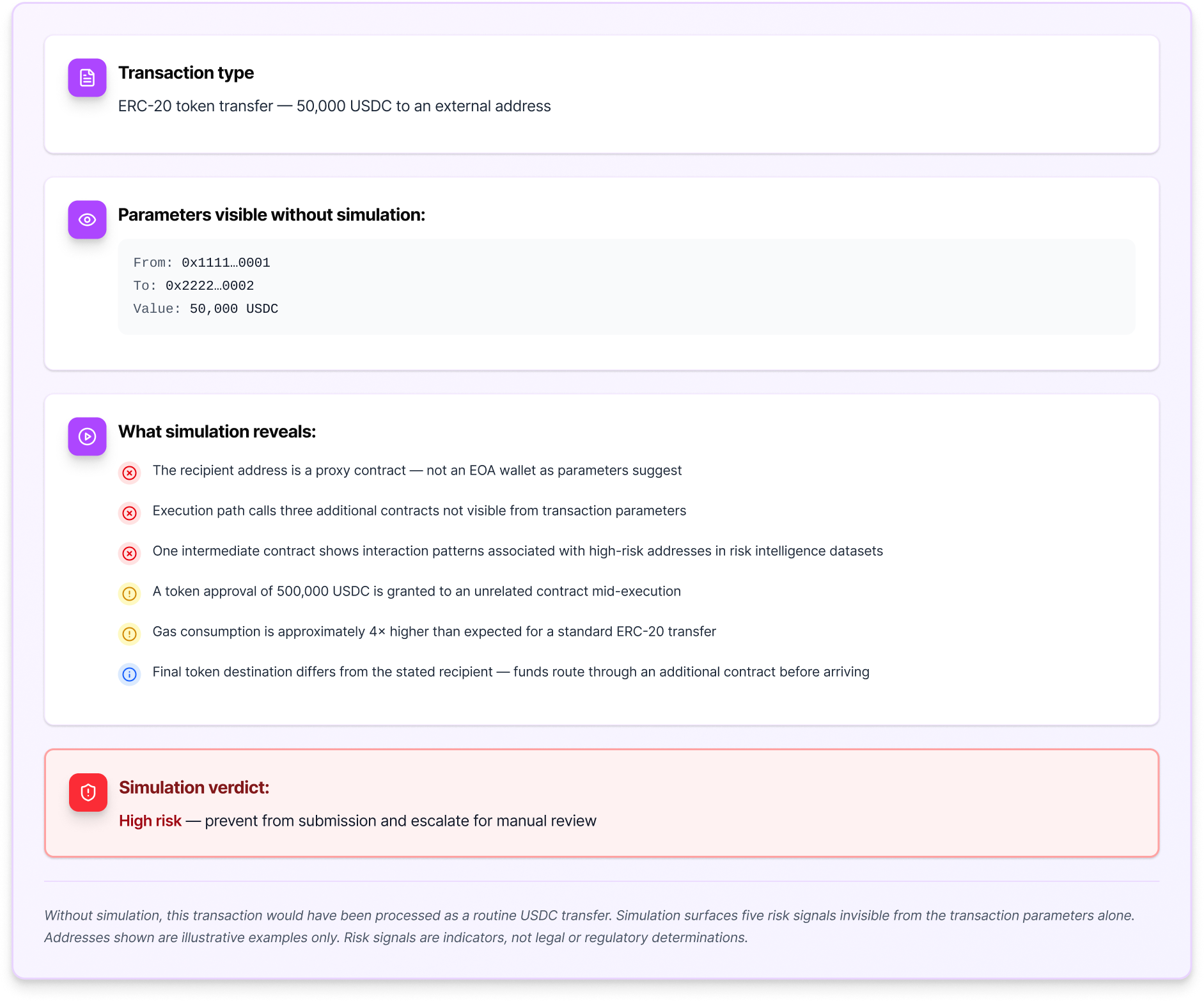
Transactions routed through Web3Firewall are simulated before broadcast within supported environments. The simulation output feeds a real-time verdict — allow, deny, or require approval — that enforces policy decisions before the transaction reaches the network. Detection without enforcement is incomplete. Web3Firewall closes that gap.

Pre-broadcast enforcement, not just analysis
Simulation results feed directly into a real-time decision engine. Transactions routed through Web3Firewall that simulate as high-risk receive an automated verdict — allow, deny, or require approval — before they are submitted. Not a reporting tool. An enforcement layer for configured workflows.

Full execution path tracing
Every function call, external contract interaction, token transfer, and state change is traced across the complete call graph within supported environments — including deeply nested cross-protocol interactions invisible from transaction parameters alone.

Integrated risk scoring
Simulation outputs are scored against Web3Firewall's risk model — combining execution path signals with wallet risk scores, high-risk address screening, and behavioral baselines to produce a unified pre-execution risk assessment.

Programmable enforcement policies
Define simulation-based enforcement policies in a no-code interface or via API. Policies can be transaction-type-specific, asset-specific, or counterparty-specific. The enforcement layer adapts to your risk framework.

Compliance-ready simulation logs
Every simulation run is logged with execution details, risk signals, verdict, and supporting evidence. These logs are designed to support regulatory reporting workflows and internal governance reviews. Nothing in these logs constitutes a legal or regulatory determination.

API integration for existing workflows
Web3Firewall's simulation API integrates into existing transaction processing pipelines — exchanges, custodians, DeFi protocols, and infrastructure providers. Designed for near real-time operational use, not batch processing. See the API documentation for performance specifications and supported environments.
Disclaimer: Web3Firewall provides risk intelligence and analysis tools. It does not provide legal, regulatory, or investment advice. Detection outputs are risk indicators designed to support human and automated decision-making within configured workflows. They are not guarantees of detection or prevention outcomes. Results depend on integration, configuration, and supported environments.