How Web3Firewall protects against off-chain trust exploitation
Request a demoWeb3Firewall is a Web3 security and compliance platform, often described as a SIEM for blockchain. It introduces a pre-execution control layer for blockchain transactions. For protocol operators, it provides pre-broadcast transaction simulation, behavioral anomaly detection, privileged function monitoring, and a programmable policy engine. Transactions routed through Web3Firewall can receive a real-time verdict, allow, deny, or require approval, that applies customer-defined policies before submission within supported environments and integrations.
This enables protocols to evaluate not just whether a transaction is valid, but whether it should be allowed to proceed given its economic and behavioral context.

Economic consistency simulation
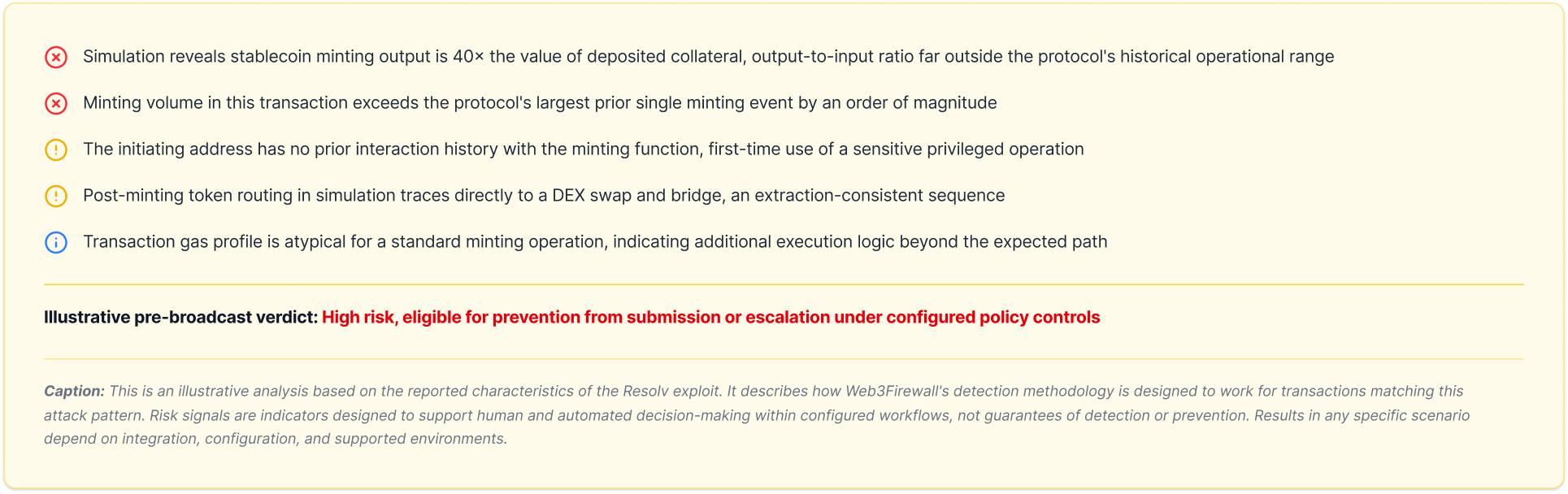
Every transaction routed through Web3Firewall is simulated before broadcast within supported environments, evaluating the full economic outcome including all asset creation, token movements, and state changes. Outputs that are disproportionate to inputs relative to the protocol's established operational patterns are surfaced as high-weight risk signals before execution.

Privileged function monitoring
Calls to sensitive contract functions, minting, ownership modification, access control changes, upgrades, are continuously monitored for anomalous usage patterns. Unusual invocation conditions, first-time callers, atypical timing, and transaction volumes outside historical norms are flagged automatically within supported environments.

Behavioral deviation detection
Protocol interactions develop behavioral baselines over time. Deviations from those baselines, unusual transaction sequences, atypical value flows, interaction patterns consistent with extraction activity, are surfaced as risk signals even when no known-bad addresses or signatures are involved.

Programmable policy engine
Define protocol-specific risk and security policies in a no-code interface or via API. Policies can be calibrated to minting ratios, collateralisation thresholds, privileged function usage patterns, and extraction-consistent flow sequences, applying customer-defined risk rules within configured workflows before submission.

Audit-ready incident records
Every simulation run, monitoring alert, and transaction verdict is logged with execution details, risk signals, and supporting evidence, providing auditable records for post-incident analysis, governance reviews, and any subsequent regulatory or legal proceedings.